What is Encryption?
Encryption is a tool that is used to ensure data security, in which data is encrypted, or encoded, so it is not able to be intercepted by a malicious third party. Cryptography is the study of coding and decoding information, often through the use of mathematics and computer science. Encryption employs cryptography techniques and algorithms in order to protect data. As technology advances, encryption methods become more vulnerable to brute force attacks, and as knowledge in math and computer science evolves, encryption methods become more vulnerable to being cracked using an algorithm.
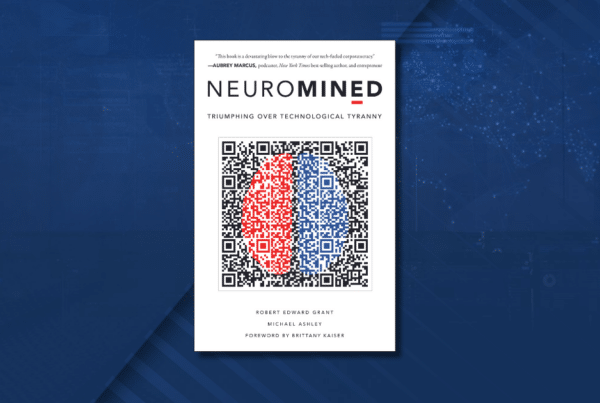
“There is a quantum-resistant solution: One-Time Pad encryption, which is viewed by cryptography experts as the most reliable method of data security. It is the world’s standard, and will be available to the world through our platform in a key compression that is outstanding and practical.”
–Robert E. Grant, CEO and Founder of Crown Sterling.
How Does Encryption Work?
Suppose there is a data set that needs to be encrypted. The original data set, which is referred to as plain text, is transformed into cipher text, a concealed version of the plain text that should not be able to be traced back to the original data set by anyone other than those who are legitimately entitled to the information in question. The vast majority of encryption algorithms involve assigning pseudo-random keys to data sets. In theory, it is impossible to intercept encrypted data without possessing the key that is distributed to the owner or other individuals entrusted to access the information. However, in reality, a malicious third party well-versed in data algorithms and equipped with resources with ample computing power could decrypt the data set without a key.
Uses of Encryption
Encryption has been used throughout history, since ancient times. Symbol replacement, a method of encryption, was used in Ancient Egypt, Greece, and Rome. However, modern encryption did not emerge until the 20th century. One of the first applications of encryption was to ensure secure military communication. As modern society has evolved into the digital age, data encryption has become ubiquitous. In 2007, the Computer Security Institute conducted a study and found that 53% of companies used encryption for data in storage and 71% of companies used encryption for data in transit. Stored data should always be encrypted in order to prevent the information from being compromised in case that the physical device is somehow intercepted. Data in transit is also protected by encryption to prevent “eavesdropping”. Another application of encryption is to make the process of deleting data more efficient. During this process, referred to as crypto-shredding, data encryption keys are overwritten in order to erase data. Although the advancement in technology has fueled the progress of encryption, the development of devices with greater computing power has posed a security threat to existing encryption methods.
Types of Encryption
There are two main types of encryption, symmetric key encryption and asymmetric key encryption. In asymmetric key encryption, there is a public key used for encryption technologies and a private key used for decryption. One the other hand, in symmetric key encryption, there is a single private key used for both encryption and decryption.
In 1977, the United States government established the Data Encryption Standard. Four years later, the government developed Triple DES, an enhancement of the original Data Encryption, which repeats the encryption and decryption process three times, as the name suggests. However, these early encryption algorithms soon became obsolete in the face of advancing technology.
There are many different types of encryption algorithms that are used today. RSA cryptography, named after MIT colleagues Ron Rivest, Adi Shamir, and Leonard Adleman, was one of the first widely used encryption algorithms that utilized public key cryptography. RSA, which was discovered in 1977, is based on factorization of extremely large semiprime numbers, where the public key is the product of two large prime numbers and the private key is of the prime factors. Likewise, Elliptic Curve Cryptography (ECC) is also a form of public key cryptography. Discovered in 1985, Elliptic Curve Cryptography (ECC) is based on solving the equation y^2 = x^3 + ax + b. In 2002, the United States government established the Advanced Encryption Standard (AES) and is still known to be one of the most robust and widely used encryption methods used today. AES Encryption is a form of symmetric key cryptography that involves an advanced version of the Rijndael block cipher. In addition, most websites use Secure Sockets Layer (SSL), which is a tool that encrypts all data that is being sent to and from a website.
Finally, One-Time Pad (OTP) cryptography is an encryption method that experts consider to be the gold standard of encryption. OTP cryptography is unable to be cracked, as long as the key is as long as the plaintext, the key is random, the key is never reused, and the key is kept secret. In most cases, a longer encryption key ensures a higher level of security. This is one of the factors that distinguished OTP cryptography from other methods of encryption. OTP cryptography was first used to facilitate military communication as securely as possible. However, OTP cryptography is not widely used today because much difficulty arises when trying to produce truly random keys. It is perceived as impractical because of the challenge of scalability (storing keys that are as long as the data set). As technology advances, encryption methods become more vulnerable to brute force attacks, and as knowledge in math and computer science evolves, encryption methods become more vulnerable to being cracked using an algorithm.
Why is Encryption Necessary?
In today’s world, where an individual’s digital identity is becoming increasingly identical to themselves, there is a growing need to protect personal information. This information includes but is not limited to text messages, phone calls, email correspondences, personal photos, bank account information, social security numbers, medical history, and credit card information. Individuals are entitled to the right to privacy and protection in order to promote their health, safety, and general well-being. While the intended use of encryption is to protect data, it can also be used to commit cyber crimes, such as ransomware attacks. Criminals commit ransomware attacks by encrypting an individual or organization’s data, and demanding a ransom in exchange for decrypting the data. In today’s world, organizations and individuals need access to their data in order to conduct business and go about their daily lives. The increasing frequency of ransomware attacks amplifies the need for better encryption methods and improvements in cybersecurity overall. As society progresses through the Age of Digitization, cybersecurity is becoming more and more crucial to the health, safety, and well being of society. For this reason, cryptography has grown greatly in importance in recent years. Encryption will continue to evolve as technology advances, until an ideal solution is found.
Crown Sterling’s Solution
Crown Sterling has already launched the Crown Sterling Chain, the world’s first layer-1 blockchain implementing OTP’s quantum-resistant solutions and the Crown Sovereign utility token (CSOV). The project also has its own “Data Bill of Rights,” which establishes digital assets as the intangible personal property of consumers under existing laws and protections in the United States, acting as the genesis block for the blockchain. CSOV is the blockchain’s native token. It allows users to participate in product offerings, including quantum-resistant encryption, NFTs, and a variety of products that Crown Sterling will be coming out with in the near future. The team is also developing a layer-2 security solution to offer its encryption protocols to other blockchains. Stay tuned and join the conversation.
About Crown Sterling Limited LLC
Leader in Data Sovereignty and provider of quantum-secure encryption, Crown Sterling empowers individuals and communities in an era of unregulated data consolidation, monopolization, and monetization by Big Tech. By leveraging next-generation encryption, blockchain technology, and decentralized digital transformation represented by Web3, we are committed to granting you complete control over your personal data and supporting the protection of free speech, assembly and choice.
The launch of Orion™ Messenger presents a quantum-secure end-to-end encrypted, uncensorable, and decentralized communications platform as a solution where sovereign individuals and communities can thrive. Unlike commonly used applications that rely on vulnerable encryption protocols, data mining practices, and other limitations, Orion is the only platform allowing for large encrypted group chat and social media communications in an unmonitored and uncensorable environment. Join the Orion Messenger waitlist.