Do we truly own our data today? Learn more about data’s value, security, and some of the transformational technology Crown Sterling offers to empower Data Sovereignty.
Some were shocked when the Economist proclaimed in 2017, “the world’s most valuable resource was data and no longer oil,” and further cited the giants that deal in data as:
“These titans—Alphabet (Google’s parent company), Amazon, Apple, Facebook and Microsoft—look unstoppable. They are the five most valuable listed firms in the world. Their profits are surging: they collectively racked up over $25bn in net profit in the first quarter of 2017. Amazon captures half of all dollars spent online in America. Google and Facebook accounted for almost all the revenue growth in digital advertising in America last year.”
Growing internet connectivity has led many companies to express greater interest in monetizing data, running analytics after collecting information, and investing in rapidly-expanding data-focused technologies like artificial intelligence and cloud computing. At best, our data is used to improve our user experience. The data can also be applied to power smart cities, train artificial intelligence, and even drive policy changes based on public sentiment. While this has helped spur innovation, it has left many worried about their digital privacy and the security of personal information, a concern that has grown due to the following examples.
In 2018, the Washington Post reported how fitness tracking application Strava was revealing sensitive information about U.S. military personnel. The outlet also noted that reporters could access the personal information of thousands of military and security personnel via the Polar fitness app.
In 2019, Facebook paid a $643,000 fine to U.K. officials for its role in the Cambridge Analytics scandal. The social media platform failed to secure personal information, allowing Cambridge Analytica to harvest the data of millions worldwide without consent.
These breaches led to a steady increase in more people calling for personal data ownership and sovereignty.
Data Privacy & Security Talks Grow
An early 2019 Insights Network survey revealed that 79% of consumers wanted compensation for shared consumer data. Senator John Kennedy (R-LA) even introduced legislation requiring social media outlets to obtain licenses to use data in the same year.
Some companies disclosed that users could submit a request to review what information the particular platform, such as a social media website, maintained for each individual.
According to a report from The Intercept, the truth is a bit hazier. Reporter Nikita Mazurov wrote about the process for Amazon to fulfill her request in March 2022. Mazurov shared, “it ultimately took about 19 days for Amazon to fulfill my data request, in stark contrast to its reported median time of 1.5 days to process a data request, as per the company’s California Consumer Privacy Act disclosure for 2020.”
Concerns with data privacy, especially in light of the Cambridge Analytica scandal, have been one of the primary calling cards of the rapidly-growing Web3 movement.

Web 3.0: Emphasis On Decentralization And Data Security
A defining feature of Web 3.0 is data sovereignty, where users themselves can take ownership over data and control who gets to profit. In the eyes of Oasis’ Linda Lu, “No entity can take users’ data for granted in Web3.”
In Web1 and Web2, users stored their data in centralized databases, resulting in the owners of said servers controlling how consumer data was used. In Web3, data storage is decentralized to remove centralized ownership and control over private data.
The concept of data sovereignty is the central element of companies like Crown Sterling, who are leveraging the focus on Web3 to build an advanced suite of encryption products and data compression technologies.
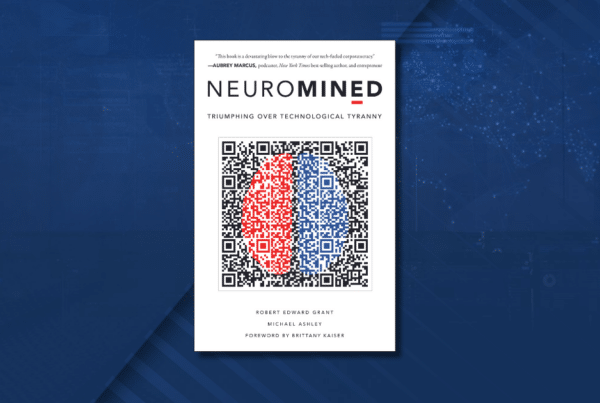
Founded and led by mathematician and ‘Philomath‘ author Robert E. Grant, the Crown Sterling team has engineered the first scalable utility for quantum-resistant One-Time Pad encryption.
Pioneering Data Sovereignty and Security
Crown Sterling believes the development of quantum computing requires secure protocols to ensure current encryption and blockchain-based systems are not vulnerable. The White House announcement at the start of the year was further evidence of growing concerns about the rise of quantum computing and its effect on data security. A recent article from Ars Technica even spoke about a potential ‘cryptopocalypse’, with the NIST announcing the requirement for new encryption standards. It talks about the current RSA encryption protocols used to encrypt our data today and how it has been proven repeatedly that these protocols can be easily decrypted using today’s technology.
“Increasing the size of the keys won’t help, either, since Shor’s algorithm, a quantum-computing technique developed in 1994 by American mathematician Peter Shor, works orders of magnitude faster in solving integer factorization and discrete logarithmic problems.” said Dan Goodin in the article.
Robert spoke at AIBC Dubai and Dcentral Austin regarding these issues and said, “The White House announced recently that every branch must be on quantum-resistant encryption within six months. That decision says a lot; this [vulnerability from quantum-computing advancement] is a real issue.”
As a leader in Data Sovereignty, Crown Sterling developed the world’s first layer-1 blockchain to implement One-Time Pad cryptography. One-Time Pad is an information-theory based encryption method that does not depend on assumptions about the computational resources of an attacker (and therefore is quantum-resistant), in contrast to conventional encryption protocols relying on prime numbers and number theory. Crown Sovereign (CSOV) utility token enables users to access the novel product suite, including quantum-resistant cryptography and NFTs, end-to-end encrypted messaging, and other future data compression technologies.
The Crown Sterling team also established a Data Bill Of Rights, “declaring digital assets to be the intangible personal property of original producers (consumers) under existing laws and protections as personal or intellectual property.” This acts as the genesis block for the Crown Sterling Chain. In the future, users will be able to encrypt personal data, including geo-location and browsing history, and convert that data into NFTs with the option to monetize it on exchanges. This furthers Crown Sterling’s vision to bring the ownership of data back into the hands of consumers.
As Web3 makes headway, companies like Crown Sterling will continue to create transformational technologies that establish and advance data sovereignty in this growing sector. Crown Sterling believes that data should belong to the original producer creator and are committed to empowering individuals to claim, protect, and control their data in an era of largely unregulated Big Tech vulnerability and monopolization.
About Crown Sterling Limited LLC
Leader in Data Sovereignty and provider of quantum-secure encryption, Crown Sterling empowers individuals and communities in an era of unregulated data consolidation, monopolization, and monetization by Big Tech. By leveraging next-generation encryption, blockchain technology, and decentralized digital transformation represented by Web3, we are committed to granting you complete control over your personal data and supporting the protection of free speech, assembly and choice.
The launch of Orion™ Messenger presents a quantum-secure end-to-end encrypted, uncensorable, and decentralized communications platform as a solution where sovereign individuals and communities can thrive. Unlike commonly used applications that rely on vulnerable encryption protocols, data mining practices, and other limitations, Orion is the only platform allowing for large encrypted group chat and social media communications in an unmonitored and uncensorable environment. Join the Orion Messenger waitlist.